CAS Threat Modeling
Be aware that this document is a DRAFT !
"Threat modeling is an approach for analyzing the security of an application" (see https://www.owasp.org/index.php/Application_Threat_Modeling). One step in the threat modeling is the creation of a dataflow diagram (DFD) of the system so that all attack surfaces can be identified.
Here are some Proposals to mitigate security risks.
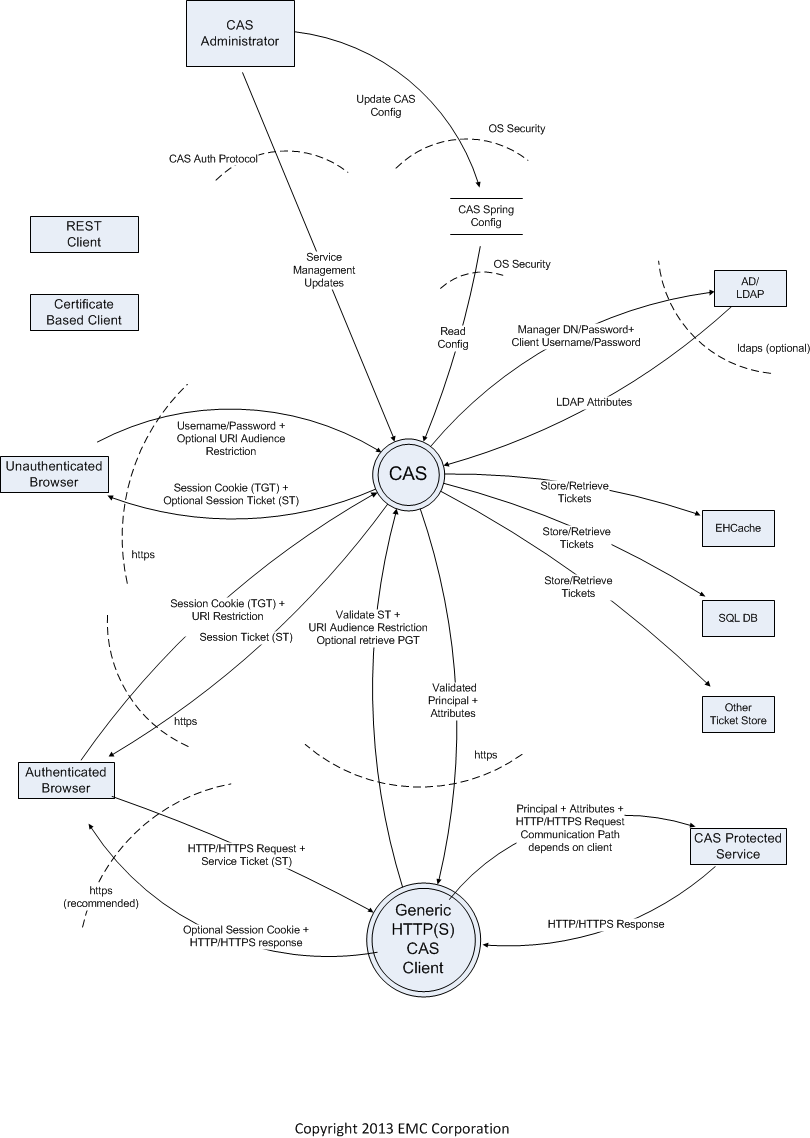
Global DFD of CAS interactions
- Visio Source File: CAS DFD.vsd
- Visio File in VDX format: CAS DFD.vdx
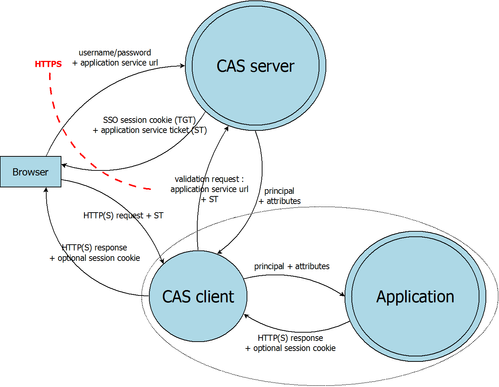
DFD of CAS protocol
- DIA format : cassecurity_protocol.dia
- VDX format : cassecurity_protocol.vdx
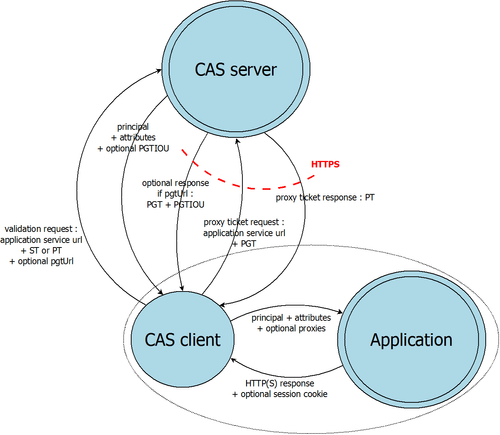
- DIA format : cassecurity_protocol_proxy.dia
- VDX format : cassecurity_protocol_proxy.vdx
Threats on "serviceValidate/samlValidate/proxyValidate" attack surface
| Identifier | Type | Threat | Mitigation |
|---|---|---|---|
| SV_1 | Information Disclosure | An ST sent over http may be intercepted by an attacker and then sent to CAS to retrieve the attributes for that user as well as the PGTIOU and the proxies. | Hardening guide to include dangers of including http services in service manager uri patterns. Change Service Manager default configuration to not generate and ST for a http based service. The current default has http://* in the list of valid services. Validate server identity using a client Cert sent in the serviceValidate call. Or make it an option in the services manager to require a client cert. Other methods could be used such as basic auth (using a shared secret) or else IP filtering. This is less secure but easier to set up. Warning in the service manager that http is dangerous. Perhaps warning in the log file. Tool to look for more misconfigurations.
|
| SV_2 | Spoofing | An ST sent over http may be intercepted by an attacker and then sent to a service to spoof the client. | Should look at the later. It is a different attack surface. |
| SV_3 | Information Disclosure | An attacker may probe for a misconfigured CAS server by asking for service ticket for various services at /login or at /serviceValidate until it finds a URI that should not be able to get tickets, but can if it can take over that URI.
| At /serviceValidate, ensure that if the ticket is not valid, then the response is always the same and does not reveal anything about the service registry. At the login URI, only disallow the call for an "invalid" service, once a user supplies a password, so that at least only authenticated users can do this probing. Or lock down an account that makes too many login calls with an invalid "service". It maybe that this cannot be mitigated because you have to support gateway access: https://secure.example.com/cas/login?gateway=true&service=https://myfishing |
| SV_4 | Information Disclosure | It is easy to write bad patterns in the services registry when using ant patterns (this info needs validation). Here is a possible example : If you define the following service : http://example.*/myService to match http://example.com/myService and http://example.fr/myService, it's a bad idea as it can be tricked by http://example.hostattacker.com/myService.
| Default to using regexp or other pattern matching that is not prone to failure. Document the pitfalls of ant matching in the security guide. |
| SV_5 | Information Disclosure | An attacker could construct a odd, but legal URI to trick the services pattern matching. See http://static.springsource.org/spring-security/site/docs/3.2.x/reference/springsecurity-single.html#request-matching for what spring security does. Here is an example of an odd, but legal path in a uri: /secure;hack=1/somefile.html;hack=2 | Ensure in the matching code that paths are normalized before matching against the service registry as spring security does. |
| SV_6 | Spoofing | There is a well-known threat to CAS clients where an unauthorized proxy may be possible if the CAS client trusts the HOST header in the request. A recently written CAS client is known to have this problem and there are probably others. | Write a security/hardening guide for CAS clients which contains all the needed advice for writing a secure CAS client in one place.
|
| SV_7 | Spoofing | An attacker could try to fool a cas client with a cleverly constructed service ticket like ticket=ST-12345%26service%3Dhttps%3A%2F%2Fbadguy.com which decodes to: ST-12345&service=https://badguy.com. If a naive client pasted this in during serviceValidate in the ticket parameter, he could be validating a ticket intended for somone else. This behavior is not observed in mod_auth_cas or the java cas client. | Ensure that all outside inputs are properly decoded and encoded when used calls to CAS or other services. Write a security/hardening guide for CAS clients which contains all the needed advice for writing a secure CAS client in one place. |
| SV_8 | DoS | An overly large ticket might cause a denial-of-service or otherwise compromise the system. (However URI's are limited in length by most implementations). | Ensure that input is validated and that overly large inputs are discarded. Write a security/hardening guide for CAS clients which contains all the needed advice for writing a secure CAS client in one place. |
Threats on "proxy callbacks" attack surface
| Identifier | Type | Threat | Mitigation |
|---|---|---|---|
| PC_1 | Information Disclosure | If HTTPS is not used, the pgtIou and pgtId (=PGT) can be stolen. | Always use HTTPS for proxy callbacks. Hopefully, this is the default in the CAS server. |
| PC_2 | Spoofing | With a stolen pgtId, the attacker can try to forge proxy tickets by trying various services on /proxy url and discover (more) user's attributes. Is it the same threat as PRO_2 ? | Limit as much as possible the services definition : not a very efficient solution, we should never reach that point ! |
| PC_3 | Information Disclosure | The pgtIou and pgtId are send as GET parameters, which can be a problem as they might be stored in logs or indexed in internal search engines... | Never log the GET parameters on the proxy callback url. Though, it might be not sufficient. Should we change the CAS protocol in the next revision (v4.0) to POST these parameters ? |
| PC_4 | DoS | A map with all pgtIou and pgtId must be saved to be able to associate the user's identity (and the pgtIou from /serviceValidate url for example) and PGT. Sending a lot of proxy callback calls with fake pgtIou and pgtId can fill the memory and cause the web application to crash. | Don't use default memory implementation. Use more advanced cache systems if they have been implemented to store pgtIou and pgtId. |
Threats on "/proxy" attack surface
| Identifier | Type | Threat | Mitigation |
|---|---|---|---|
| PRO_1 | Information Disclosure | If HTTPS is not used, the PGT can be stolen, which is extremely critical as it represents a SSO identity. | Always use HTTPS for /proxy url. |
| PRO_2 | Spoofing | The attacker can generate proxy tickets for other services and discover (more) user's attributes. | Limit as much as possible the services definition : not a very efficient solution, we should never reach that point ! |
| PRO_3 | Information disclosure | The targetService and pgtId are send as GET parameters, which can be a problem as they might be stored in logs or indexed in internal search engines... | Never log the GET parameters on the /proxy url. Though, it might be not sufficient. Should we change the CAS protocol in the next revision (v4.0) to POST these parameters ? |
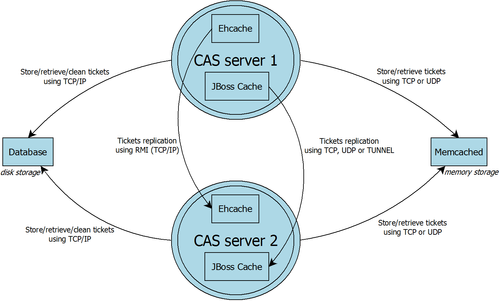
DFD of CAS tickets storage
- DIA format : cassecurity_tickets_storage_1.1.dia
- VDX format : cassecurity_tickets_storage_1.1.vdx
Threats on storage
| Identifier | Type | Threat | Mitigation |
|---|---|---|---|
| STO_1 | Information Disclosure | Attack on network : For memcached/database (whatever the number of nodes) or Ehcache/JBoss cache (on multinodes), data are transfered between nodes using TCP. These data can be intercepted and scanned to know which TGT is linked to which identity. | Add an entry to the hardening guide to indicate that single node CAS deployments should prefer to use Ehcache since the communication between CAS and Ehcache will be internal to the JVM. Also, disk persistence should preferably turned off to avoid saving the sensitive data to the disk. Add an entry to the hardening guide to indicate that the ehcache/jboss replication or the external database/memcached should either be restricted to a private network, or else run over SSL/TLS to protect the data in transport. When using ehcache, consider using JGroups for communication which has support for encryption. Encryption/hashing scheme:
|
| STO_2 | Information Disclosure | Attack on disk : For database/Ehcache cache storage on disk, an attacker can read the content of the stored files and find the identities and their associated TGT. | Add an entry to the hardening guide to indicate that for single node CAS, disk persistence should preferably turned off to avoid saving the sensitive data to the disk. Add an entry to the hardening guide to indicate that the any disk based memory should either be restricted to a private storage, or else encrypt data on disk. Should we really use Ehcache to store data on disks : not really performant and secure ? For database, some encryption mechanism can be enabled on disk stored data. |
| STO_3 | Information Disclosure | Attack on memory: Various tools can scan the memory of other processes. We should try to do things to protect the data in memory and hash and encrypt data as soon as possible. This may involve interactions with the garbage collector, including removing sensitive data in the clear so that the young garbage collector can handle this sensitive data rather than relying on the full garbage collection to remove this data.
| Use best practices to remove unencrypted, unhashed sensitive data from memory as soon as possible. |
| STO_4 | Spoofing | The attacker can generate false data and send them to the storage system. | Use hash / cryptographic algorithm to prevent attackers from being able to forge keys and store data. |
Threats on CAS interaction with authentication sources (e.g. LDAP or username/password DB)
| Identifier | Type | Threat | Mitigation |
|---|---|---|---|
| STO_1 | Information Disclosure | Attack on network : Username/password can be intercepted in transit These data can be intercepted and scanned to know which TGT is linked to which identity. | Add an entry to the hardening guide to LDAP deployments should prefer to use ldaps + certification validation unless the calls are guaranteed to be traveling over an untrusted network with an internal dns. If a database is being used, recommend to turn on SSL/TLS and certificate validation for the Database endpoint to ensure that the username is not being passed on to an intruder the calls are guaranteed to be traveling over an untrusted network with an internal dns. |
| STO_2 | Information Disclosure | Attack on disk : Attacker could steal the list of username/passwords from an insecure database. | Add an entry to the hardening guide to indicate that for single node CAS, disk persistence should preferably turned off to avoid saving the sensitive data to the disk. Add an entry to the hardening guide to indicate that the any disk based memory should either be restricted to a private storage, or else encrypt data on disk. Should we really use Ehcache to store data on disks : not really performant and secure ? For database, some encryption mechanism can be enabled on disk stored data. |
| STO_3 | Information Disclosure | Attack on memory: Various tools can scan the memory of other processes. We should try to do things to protect the data in memory and hash and encrypt data as soon as possible. This may involve interactions with the garbage collector, including removing sensitive data in the clear so that the young garbage collector can handle this sensitive data rather than relying on the full garbage collection to remove this data.
| Use best practices to remove unencrypted, unhashed sensitive data from memory as soon as possible. |
| STO_4 | Spoofing | The attacker can generate false data and send them to the storage system. | Use hash / cryptographic algorithm to prevent attackers from being able to forge keys and store data. |